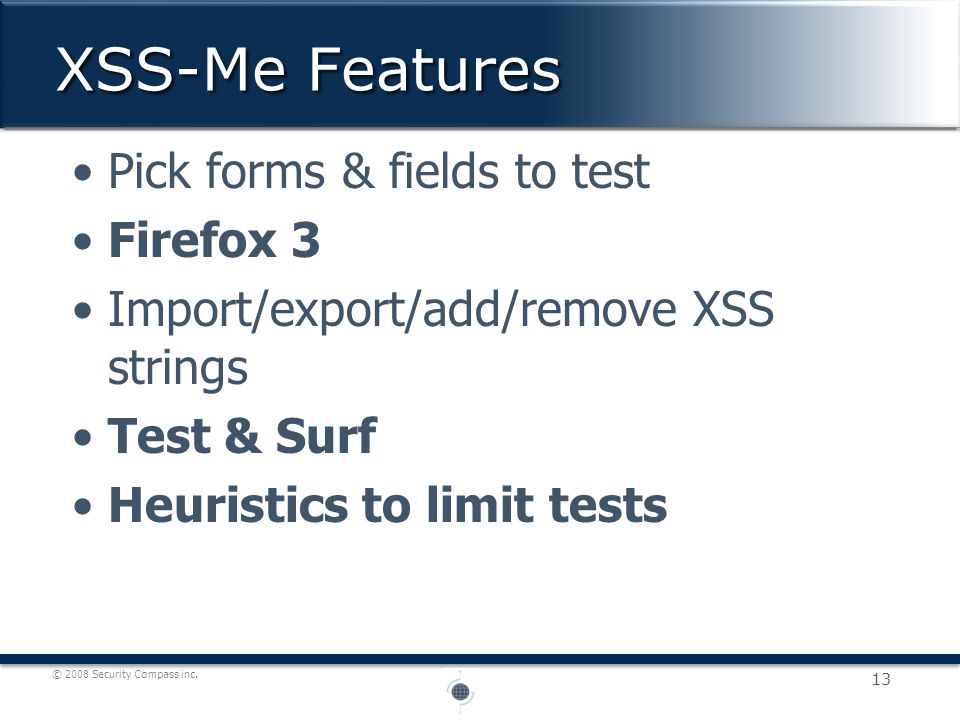
Firefox add-ons are useful for penetration testers and security analysts. These penetration testing add-ons helps in performing different kinds of attacks, and modify request headers direct from the browser. This way, it reduces the use of a separate tool for most of the penetration testing related tasks. Aug 02, 2012 NoScript XSS filter: this popular Firefox add on comes with an XSS filter. However, the extension interface does not allow developers to predicate on the content of scripts; therefore, NoScript can only detect suspicious patterns in the URL that may represent HTML or JavaScript code, without actually confirming that the maliocious code appears. Forcing Firefox to Execute XSS Payloads during 302 Redirects. Submitted by quentin on Wed, - 14:49. Initial Discovery. During a recent engagement I identified an open redirect where a GET parameter would be reflected as-is in the HTTP response Location header without any kind of sanitization. Something similar to this. Tamper data is a great tool to view and modify HTTP/HTTPS headers and post. XSS-Me is the Exploit-Me tool used to test for reflected Cross-Site Scripting (XSS). It does NOT currently test for stored XSS. The tool works by submitting your HTML forms and substituting the form value with strings that are representative of an XSS attack.
NoScript 10 'Quantum' resources
NoScript also provides the most powerful anti-XSS and anti-Clickjacking protection ever available in a browser.
NoScript's unique whitelist based pre-emptive script blocking approach prevents exploitation of security vulnerabilities (known, such as Meltdown or Spectre, and even not known yet!) with no loss of functionality...
You can enable JavaScript, Java and plugin execution for sites you trust with a simple left-click on the NoScript status bar icon (look at the picture), or using the contextual menu, for easier operation in popup statusbar-less windows.
Watch the 'Block scripts in Firefox' video by cnet.
Staying safe has never been so easy!
Experts will agree: Firefox is really safer with NoScript!
V. 11.1.6 - Quantum Security for everyone!
If you find any bug or you'd like an enhancement, please report here or here. Many thanks!
Main good news
- Android-compatible prompts for XSS warnings and click-to-play.
- Several improvements to handling of file:// pages.
- Discoverable option to force site-leaking UI in PBM/Incognito.
- Full UI keyboard-based navigation:
- Alt+Shift+N
- start
- Arrows/Tab
- move
- DEL/BKSPC/0
- DEFAULT
- +
- TRUSTED
- -
- UNTRUSTED
- C
- CUSTOM
- T
- Temp
- S
- HTTPS-lock
- HOME
- jump to the toolbar
- ESC/ENTER
- Close the UI
- R
- Reload current page without closing the UI
- Shift+G
- Globally disable restrictions
- Shift+T
- Disable restrictions on this tab
- P
- Set all on this page to Temp. TRUSTED
- F
- Forget temporary permissions
- Operating on Incognito tabs prevents you from setting permanent permissions to avoid privacy leaks on disk (see https://trac.torproject.org/projects/tor/ticket/29957).
- Improved Firefox Preview (Fenix) / Firefox for Android UI.
- Completely asynchronous XSS Filter in its dedicated process
- Several new and updated translations, thanks to the Localization Lab / OTF NoScript Transifex project.
- 'Override Tor Browser Security Level preset' option offers more flexibility to NoScript+Tor power users.
Experts do agree...
03/10/2014, Edward Snowden endorses NoScript as a countermeasure against state Surveillance State.
08/06/2008, 'I'd love to see it in there.' (Window Snyder, 'Chief Security Something-or-Other' at Mozilla Corp., interviewed by ZDNet about 'adding NoScript functionality into the core browser').
03/18/2008, 'Consider switching to the Firefox Web browser with the NoScript plug-in. NoScript selectively, and non-intrusively, blocks all scripts, plug-ins, and other code on Web pages that could be used to attack your system during visits' (Rich Mogull on TidBITS, Should Mac Users Run Antivirus Software?).
11/06/2007, Douglas Crockford, world-famous JavaScript advocate and developer of JSON (one of the building blocks of Web 2.0), recommends using NoScript.
03/16/2007, SANS Internet Storm Center, the authoritative source of computer security related wisdom, runs a front-page Ongoing interest in Javascript issues diary entry by William Stearns just to say 'Please, use NoScript' :)
Actually, NoScript has been recommended several times by SANS, but it's nice to see it mentioned in a dedicated issue, rather than as a work-around for specific exploits in the wild. Many thanks, SANS!
05/31/2006, PC World's The 100 Best Products of the Year list features NoScript at #52!
Many thanks to PC World, of course, for grokking NoScript so much, and to IceDogg who kindly reported these news...
In the press...
- CNET News: 'Giorgio Maone's NoScript script-blocking plug-in is the one-and-only Firefox add-on I consider mandatory.' (March 9, 2009, Dennis O'Reilly, Get a new PC ready for everyday use)
- Forbes: 'The real key to defeating malware isn't antivirus but approaches like Firefox's NoScript plug-in, which blocks Web pages from running potentially malicious programs' (Dec 11, 2008, Andy Greenberg, Filter The Virus Filters).
- PC World: Internet Explorer 7 Still Not Safe Enough because it doesn't act like 'NoScript [...] an elegant solution to the problem of malicious scripting' (cite bite)
- New York Times: '[...] NoScript, a plug-in utility, can limit the ability of remote programs to run potentially damaging programs on your PC', (Jan 7, 2007, John Markoff, Tips for Protecting the Home Computer).
- PC World's Ten Steps Security features using NoScript as step #6. (cite bite)
- The Washington Post security blog compares MSIE 'advanced' security features (like so called 'Zones') to Firefox ones and recommends NoScript adoption as the safest and most usable approach. (cite bite)
Contributor(s): Jim Manico, Jeff Williams, Dave Wichers, Adar Weidman, Roman, Alan Jex, Andrew Smith, Jeff Knutson, Imifos, Erez Yalon, kingthorin
Overview
Cross-Site Scripting (XSS) attacks are a type of injection, in whichmalicious scripts are injected into otherwise benign and trustedwebsites. XSS attacks occur when an attacker uses a web application tosend malicious code, generally in the form of a browser side script, toa different end user. Flaws that allow these attacks to succeed arequite widespread and occur anywhere a web application uses input from auser within the output it generates without validating or encoding it.
An attacker can use XSS to send a malicious script to an unsuspectinguser. The end user’s browser has no way to know that the script shouldnot be trusted, and will execute the script. Because it thinks thescript came from a trusted source, the malicious script can access anycookies, session tokens, or other sensitive information retained by thebrowser and used with that site. These scripts can even rewrite thecontent of the HTML page. For more details on the different types of XSSflaws, see: Types of Cross-Site Scripting.
Related Security Activities
How to Avoid Cross-site scripting Vulnerabilities
- OWASP Development Guide article on Data Validation
- OWASP Development Guide article on Phishing
How to Review Code for Cross-site scripting Vulnerabilities
See the OWASP Code Review Guide.
How to Test for Cross-site scripting Vulnerabilities
See the latest OWASP Testing Guide article on how totest for the various kinds of XSS vulnerabilities.
Description
Cross-Site Scripting (XSS) attacks occur when:
- Data enters a Web application through an untrusted source, most frequently a web request.
- The data is included in dynamic content that is sent to a web user without being validated for malicious content.
The malicious content sent to the web browser often takes the form of asegment of JavaScript, but may also include HTML, Flash, or any othertype of code that the browser may execute. The variety of attacks basedon XSS is almost limitless, but they commonly include transmittingprivate data, like cookies or other session information, to theattacker, redirecting the victim to web content controlled by theattacker, or performing other malicious operations on the user’s machineunder the guise of the vulnerable site.
Stored and Reflected XSS Attacks
XSS attacks can generally be categorized into two categories: stored andreflected. There is a third, much less well-known type of XSS attackcalled DOM Based XSS that is discussedseparately here.
Stored XSS Attacks
Stored attacks are those where the injected script is permanently storedon the target servers, such as in a database, in a message forum,visitor log, comment field, etc. The victim then retrieves the maliciousscript from the server when it requests the stored information. StoredXSS is also sometimes referred to as Persistent or Type-I XSS.
Reflected XSS Attacks

Reflected attacks are those where the injected script is reflected offthe web server, such as in an error message, search result, or any otherresponse that includes some or all of the input sent to the server aspart of the request. Reflected attacks are delivered to victims viaanother route, such as in an e-mail message, or on some other website.When a user is tricked into clicking on a malicious link, submitting aspecially crafted form, or even just browsing to a malicious site, theinjected code travels to the vulnerable web site, which reflects theattack back to the user’s browser. The browser then executes the codebecause it came from a “trusted” server. Reflected XSS is also sometimesreferred to as Non-Persistent or Type-II XSS.
Other Types of XSS Vulnerabilities
In addition to Stored and Reflected XSS, another type of XSS, DOM BasedXSS was identified by Amit Kleinin 2005. OWASPrecommends the XSS categorization as described in the OWASP Article:Types of Cross-Site Scripting, which covers allthese XSS terms, organizing them into a matrix of Stored vs. ReflectedXSS and Server vs. Client XSS, where DOM Based XSS is a subset of ClientXSS.
XSS Attack Consequences
The consequence of an XSS attack is the same regardless of whether it isstored or reflected (or DOM Based). Thedifference is in how the payload arrives at the server. Do not be fooledinto thinking that a “read-only” or “brochureware” site is notvulnerable to serious reflected XSS attacks. XSS can cause a variety ofproblems for the end user that range in severity from an annoyance tocomplete account compromise. The most severe XSS attacks involvedisclosure of the user’s session cookie, allowing an attacker to hijackthe user’s session and take over the account. Other damaging attacksinclude the disclosure of end user files, installation of Trojan horseprograms, redirect the user to some other page or site, or modifypresentation of content. An XSS vulnerability allowing an attacker tomodify a press release or news item could affect a company’s stock priceor lessen consumer confidence. An XSS vulnerability on a pharmaceuticalsite could allow an attacker to modify dosage information resulting inan overdose. For more information on these types of attacks seeContent_Spoofing.
How to Determine If You Are Vulnerable
XSS flaws can be difficult to identify and remove from a webapplication. The best way to find flaws is to perform a security reviewof the code and search for all places where input from an HTTP requestcould possibly make its way into the HTML output. Note that a variety ofdifferent HTML tags can be used to transmit a malicious JavaScript.Nessus, Nikto, and some other available tools can help scan a websitefor these flaws, but can only scratch the surface. If one part of awebsite is vulnerable, there is a high likelihood that there are otherproblems as well.
How to Protect Yourself
The primary defenses against XSS are described in the OWASP XSS Prevention CheatSheet.
Also, it’s crucial that you turn off HTTP TRACE support on all webservers. An attacker can steal cookie data via Javascript even whendocument.cookie is disabled or not supported by the client. This attackis mounted when a user posts a malicious script to a forum so whenanother user clicks the link, an asynchronous HTTP Trace call istriggered which collects the user’s cookie information from the server,and then sends it over to another malicious server that collects thecookie information so the attacker can mount a session hijack attack.This is easily mitigated by removing support for HTTP TRACE on all webservers.
The OWASP ESAPI project has produced a set ofreusable security components in several languages, including validationand escaping routines to prevent parameter tampering and the injectionof XSS attacks. In addition, the OWASP WebGoat Project trainingapplication has lessons on Cross-Site Scripting and data encoding.
Alternate XSS Syntax
XSS Using Script in Attributes
XSS attacks may be conducted without using <script>...</script>tags. Other tags will do exactly the same thing, for example:<body onload=alert('test1')> or other attributes like: onmouseover, onerror.
onmouseover
<b onmouseover=alert('Wufff!')>click me!</b>
onerror
<img src='http://url.to.file.which/not.exist' onerror=alert(document.cookie);>
XSS Using Script Via Encoded URI Schemes
If we need to hide against web application filters we may try to encodestring characters, e.g.: a=A (UTF-8) and use it in IMG tags:
<IMG SRC=jAvascript:alert('test2')>
There are many different UTF-8 encoding notations what give us even morepossibilities.
XSS Using Code Encoding
We may encode our script in base64 and place it in META tag. This way weget rid of alert() totally. More information about this method can befound in RFC 2397
These and others examples can be found at the OWASP XSS Filter Evasion Cheat Sheet which is a trueencyclopedia of the alternate XSS syntax attack.
Examples
Cross-site scripting attacks may occur anywhere that possibly malicioususers are allowed to post unregulated material to a trusted website forthe consumption of other valid users.
The most common example can be found in bulletin-board websites whichprovide web based mailing list-style functionality.
Example 1
The following JSP code segment reads an employee ID, eid, from an HTTPrequest and displays it to the user.
The code in this example operates correctly if eid contains onlystandard alphanumeric text. If eid has a value that includesmeta-characters or source code, then the code will be executed by theweb browser as it displays the HTTP response.
Initially, this might not appear to be much of a vulnerability. Afterall, why would someone enter a URL that causes malicious code to run ontheir own computer? The real danger is that an attacker will create themalicious URL, then use e-mail or social engineering tricks to lurevictims into visiting a link to the URL. When victims click the link,they unwittingly reflect the malicious content through the vulnerableweb application back to their own computers. This mechanism ofexploiting vulnerable web applications is known as Reflected XSS.
Example 2
The following JSP code segment queries a database for an employee with agiven ID and prints the corresponding employee’s name.

Xss Me For Firefox Bookmarks
As in Example 1, this code functions correctly when the values of nameare well-behaved, but it does nothing to prevent exploits if they arenot. Again, this code can appear less dangerous because the value ofname is read from a database, whose contents are apparently managed bythe application. However, if the value of name originates fromuser-supplied data, then the database can be a conduit for maliciouscontent. Without proper input validation on all data stored in thedatabase, an attacker can execute malicious commands in the user’s webbrowser. This type of exploit, known as Stored XSS, is particularlyinsidious because the indirection caused by the data store makes it moredifficult to identify the threat and increases the possibility that theattack will affect multiple users. XSS got its start in this form withwebsites that offered a “guestbook” to visitors. Attackers would includeJavaScript in their guestbook entries, and all subsequent visitors tothe guestbook page would execute the malicious code.
As the examples demonstrate, XSS vulnerabilities are caused by code thatincludes unvalidated data in an HTTP response. There are three vectorsby which an XSS attack can reach a victim:
- As in Example 1, data is read directly from the HTTP request andreflected back in the HTTP response. Reflected XSS exploits occurwhen an attacker causes a user to supply dangerous content to avulnerable web application, which is then reflected back to the userand executed by the web browser. The most common mechanism fordelivering malicious content is to include it as a parameter in aURL that is posted publicly or e-mailed directly to victims. URLsconstructed in this manner constitute the core of many phishingschemes, whereby an attacker convinces victims to visit a URL thatrefers to a vulnerable site. After the site reflects the attacker’scontent back to the user, the content is executed and proceeds totransfer private information, such as cookies that may includesession information, from the user’s machine to the attacker orperform other nefarious activities.
- As in Example 2, the application stores dangerous data in a databaseor other trusted data store. The dangerous data is subsequently readback into the application and included in dynamic content. StoredXSS exploits occur when an attacker injects dangerous content into adata store that is later read and included in dynamic content. Froman attacker’s perspective, the optimal place to inject maliciouscontent is in an area that is displayed to either many users orparticularly interesting users. Interesting users typically haveelevated privileges in the application or interact with sensitivedata that is valuable to the attacker. If one of these usersexecutes malicious content, the attacker may be able to performprivileged operations on behalf of the user or gain access tosensitive data belonging to the user.
- A source outside the application stores dangerous data in a databaseor other data store, and the dangerous data is subsequently readback into the application as trusted data and included in dynamiccontent.
Attack Examples
Example 1: Cookie Grabber
If the application doesn’t validate the input data, the attacker caneasily steal a cookie from an authenticated user. All the attacker hasto do is to place the following code in any posted input(ie: messageboards, private messages, user profiles):
The above code will pass an escaped content of the cookie (according toRFC content must be escaped before sending it via HTTP protocol with GETmethod) to the evil.php script in “cakemonster” variable. The attackerthen checks the results of their evil.php script (a cookie grabber scriptwill usually write the cookie to a file) and use it.
Error Page Example
Let’s assume that we have an error page, which is handling requests fora non existing pages, a classic 404 error page. We may use the codebelow as an example to inform user about what specific page is missing:
Let’s see how it works: http://testsite.test/file_which_not_existIn response we get: Not found: /file_which_not_exist
Now we will try to force the error page to include our code: http://testsite.test/<script>alert('TEST');</script>The result is: Not found: / (but with JavaScript code <script>alert('TEST');</script>)
We have successfully injected the code, our XSS! What does it mean? Forexample, that we may use this flaw to try to steal a user’s sessioncookie.
Related Attacks
Related Vulnerabilities
- OWASP Development Guide article on Data Validation
- OWASP Development Guide article on Phishing
Xss Me Plugin For Firefox
Related Controls
References
Xss Me For Firefox Windows 10
- OWASP’s XSS (Cross Site Scripting) Prevention Cheat Sheet
- OWASP XSS Filter Evasion Cheat Sheet
- XSSed - Cross-Site Scripting (XSS) Information and Mirror Archive of Vulnerable Websites